Trusted by Compliance & Risk Teams Worldwide
IT risk changes faster than most teams can respond
Ransomware, data privacy failures, and AI-driven risk are accelerating. The issue isn’t awareness – it’s visibility, prioritization, and control.
Take control of your IT risk exposure
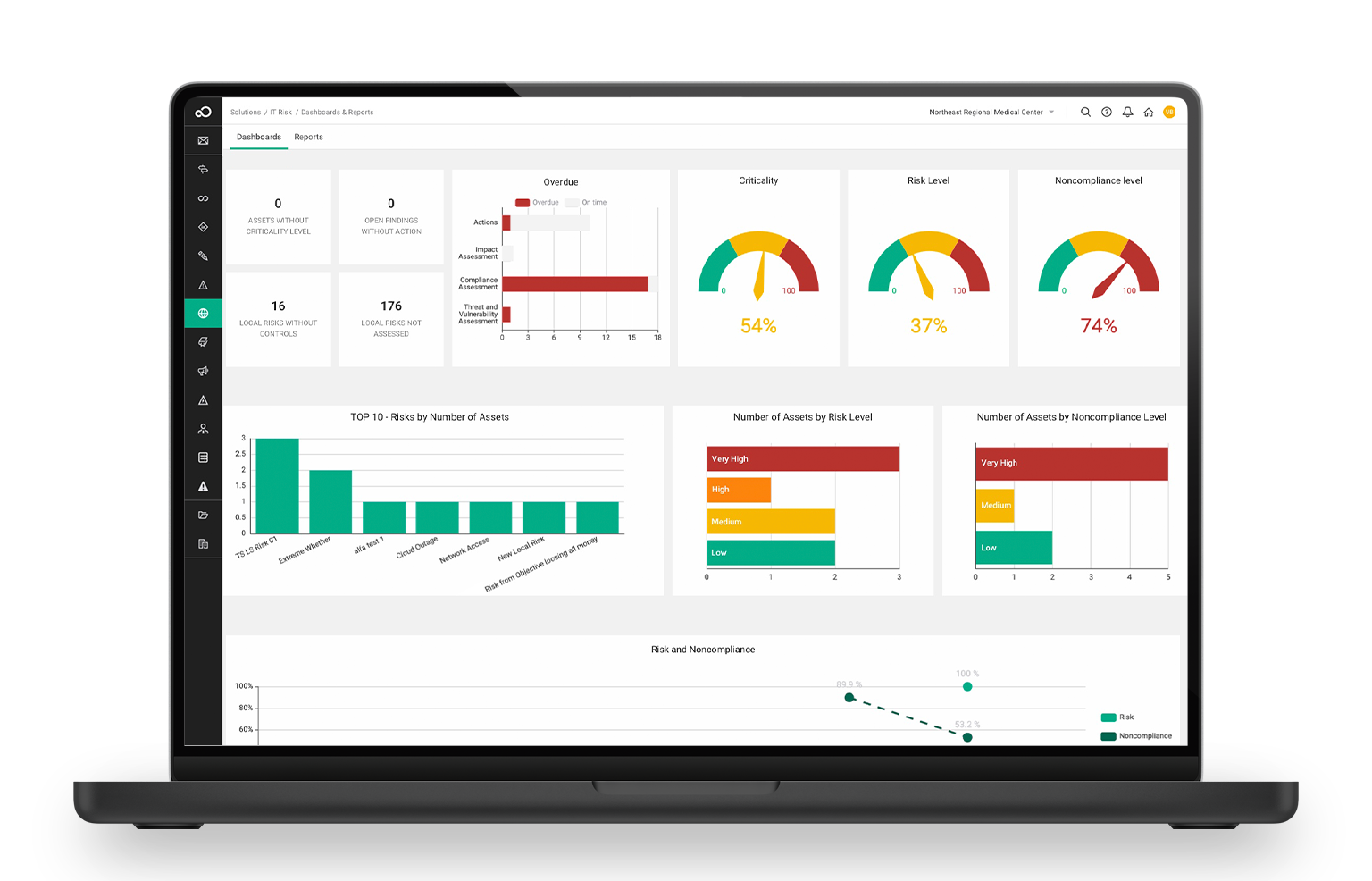
Manage IT risk across complex, fast-changing environments
Connect risk data, controls, and assessments across your IT landscape to gain a real-time view of exposure.
Explore The Capabilities
“SAI360 centralizes security and compliance audits, which is key for IT oversight.”
-Verified User in Insurance, G2 Review
Built for modern IT Risk management teams
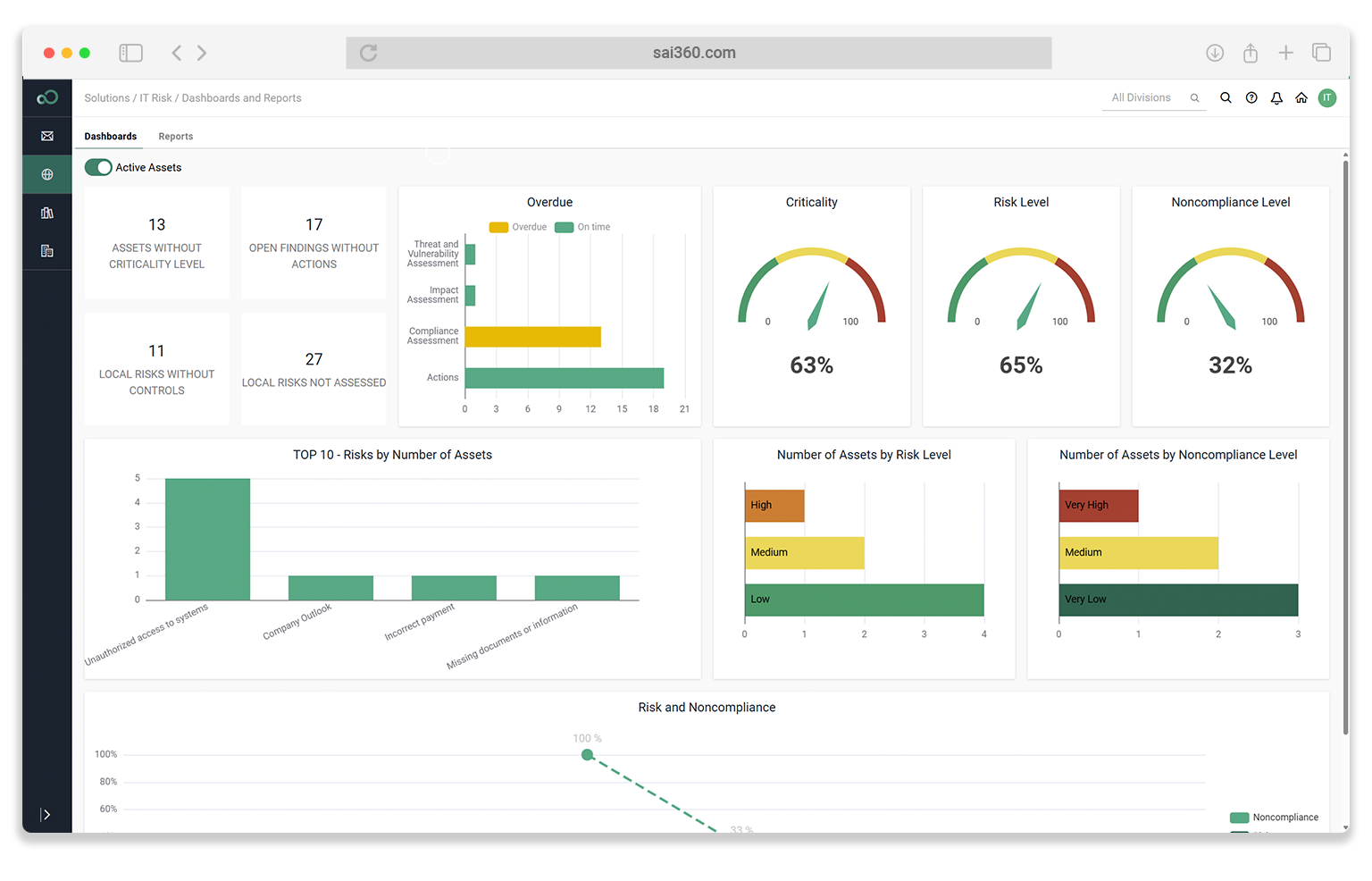
Most teams lack a clear view of IT risk across their environment.
SAI360 brings it into a single system, using AI to help teams act faster.
See How SAI360 Helps Teams Manage IT Risk
Book a 30-minute demo to see how SAI360 helps teams identify, assess, monitor, and respond to IT risk.